Protect data in use with hardware enclaves
Process sensitive data safely on bare-metal servers featuring hardware enclaves. Your information stays protected during processing, with no exposure to the OS, the network or third parties.

Secure your data at every step
Sensitive data must not only be protected at rest or in transit. It also needs protection in use — where the risk is highest.
With confidential computing you:
- isolate data in memory
- block any unauthorised access
- guarantee confidentiality even in shared environments
This is essential for demanding sectors such as finance, healthcare and AI.
High performance, controlled cost
Performance / security balance
Get powerful servers with advanced security mechanisms built in. Protect your data without sacrificing application performance.
Predictable costs
Essentials included: bandwidth, anti-DDoS protection, IP addresses and external storage. Keep a clear view of your spend.
An adaptable environment
Install whichever OS and tools fit your needs. Configure secure environments freely.
Scalable infrastructure
Run multiple sensitive workloads on the same server. Grow your resources as projects evolve.
Chargement du catalogue…
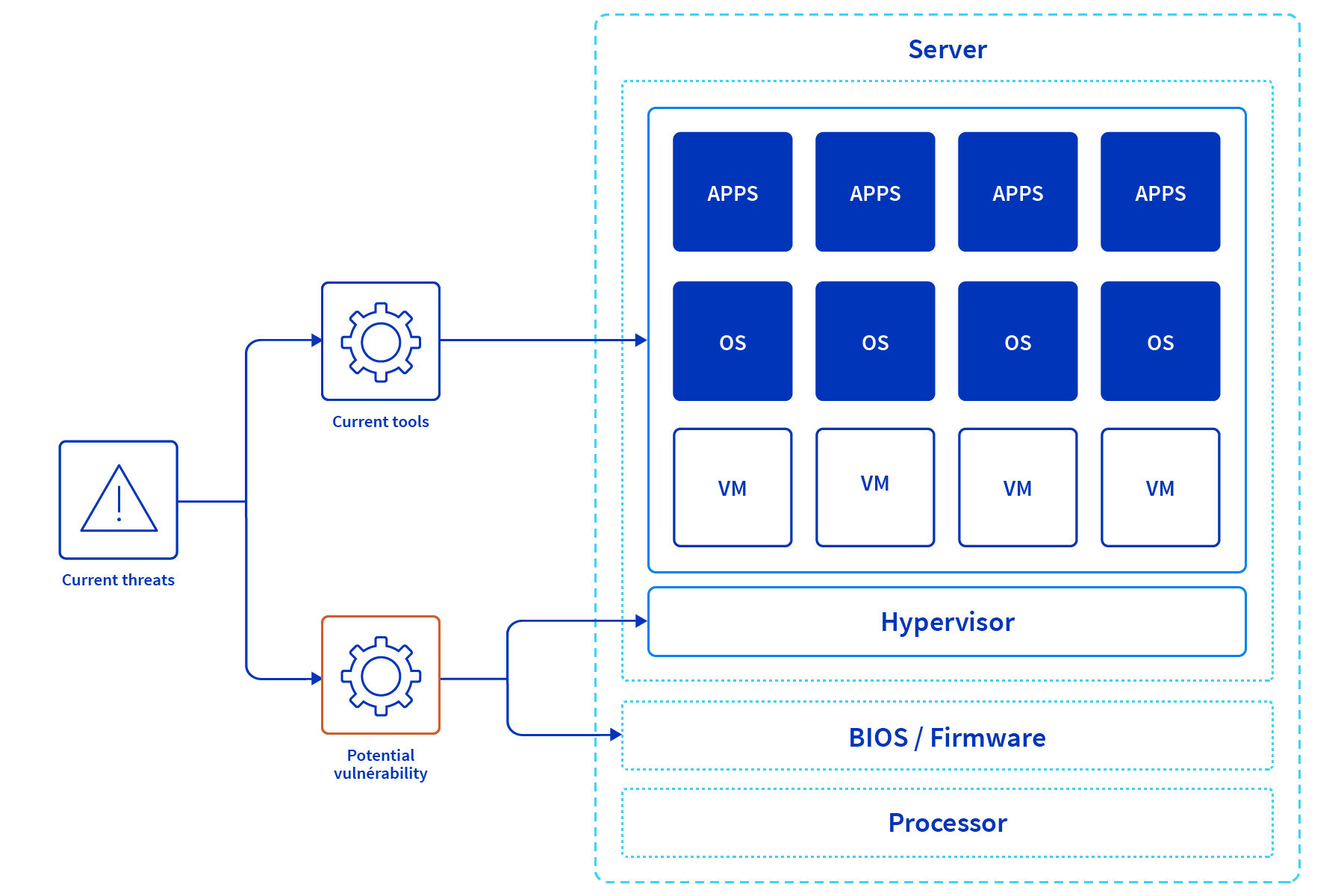
Hardware protection — without trade-offs
Activate confidential-computing technologies in just a few clicks from your customer space:
- Intel® SGX isolates code and data at the application level
- AMD Infinity Guard protects memory and virtual machines
Hardware enclaves: full isolation for data in use
Hardware enclaves create a secure zone directly inside the processor.
Code and data executed there are fully isolated, invisible to the operating system, inaccessible to the hypervisor and protected even from administrative access.
On supported servers you enable:
- Intel® SGX for secure applications
- AMD Infinity Guard for memory and VM encryption
Available options and services:
- unmetered public and private bandwidth
- advanced memory and storage options
- Intel® SGX
- AMD Infinity Guard
Does confidential computing replace traditional encryption?
No — it complements it. Encryption at rest protects stored data, encryption in transit secures network exchanges, and confidential computing protects data in use. All three are needed for end-to-end security.
What does it bring to federated learning?
The model trains inside a secure enclave. Data stays local and is never exposed, even during aggregation.
What security guarantees apply?
The datacenters meet several standards (ISO, GDPR). Data is hosted in Europe with a high level of compliance.
Is it compatible with virtualisation?
Yes. AMD Infinity Guard protects virtual machines while Intel® SGX secures applications.
How do I verify enclaves are working?
Dedicated tools let you test and validate enclave activation. Configuration can be tweaked from your customer space.